A Time to Strengthen Cyber Defenses
In today’s digital age, our lives are intricately intertwined with the internet, making us more vulnerable to cyber threats than ever. This October, as we celebrate Cyber Security Awareness Month, we must emphasize the significance of cybersecurity education, data protection, multi-factor authentication (MFA), and other critical aspects of safeguarding our digital lives. Let’s delve into the key topics surrounding Cyber Security Awareness Month and explore how we can bolster our cyber defenses.
The Significance of Cyber Security Awareness Month
Cyber Security Awareness Month, observed globally, is a dedicated time for raising awareness about the Importance of Cybersecurity. It provides individuals and organizations a valuable opportunity to focus on cybersecurity education and training. The month serves as a reminder that cybersecurity is not merely an IT concern but an issue that affects every facet of our lives, from personal data protection to corporate security solutions.
To start our conversation, it’s vital to understand the following core elements that contribute to cyber resilience.
- Data Protection
- Internet Safety and Digital Citizenship
- Acknowledge and report Cyber Threats
- Multi-Factor Authentication
Data Protection
Data is the lifeblood of the digital age, and protecting it is paramount. Whether it’s your personal information or sensitive corporate data, securing this information is critical. Data breaches can result in devastating consequences, such as identity theft, financial losses, and reputational damage. Therefore, in Cyber Security Awareness Month, we must emphasize the importance of robust data protection measures.
Organizations must implement data encryption, access controls, and regular data backups to mitigate data-related risks. Individuals can contribute by practicing good data hygiene, such as using strong, unique passwords, regularly updating software, and being cautious about sharing personal information online.

Internet Safety and Digital Citizenship
Beyond businesses, individuals also play a crucial role in maintaining a secure digital ecosystem. Practicing good internet safety and demonstrating responsible digital citizenship is essential. That means being cautious about what we share online, being mindful of the sources of information we engage with, and treating others with respect in the digital realm.
We can collectively contribute to a safer online environment by promoting Internet Safety and digital citizenship. Cyber Security Awareness Month serves as a timely reminder to cultivate these behaviors.
Acknowledge and Report Cyber Threats
Cyber threats are constantly evolving, becoming more sophisticated and widespread. Threat actors target individuals, businesses, and governments with malicious activities, including phishing, ransomware, and data breaches. To protect against these Cyber Threats, staying informed and proactive is essential.
Threat intelligence plays a pivotal role in understanding the evolving cyber threat landscape. It involves collecting and analyzing data to identify potential threats, vulnerabilities, and attack trends. During Cyber Security Awareness Month, it is vital to encourage adopting Threat Intelligence practices in organizations to anticipate and mitigate cyber risks effectively.
Multi-Factor Authentication
One of the most effective tools in the fight against cyber threats is Multi-Factor Authentication (MFA). MFA enhances security by requiring users to provide multiple forms of identification before granting access to their accounts. This extra layer of protection makes it significantly harder for cybercriminals to gain unauthorized access.
During Cyber Security Awareness Month, it’s crucial to promote the adoption of MFA among individuals and businesses. This simple but effective security measure can prevent unauthorized access to email accounts, social media profiles, and corporate networks.
The Importance of Multi-Factor Authentication
User-Friendly:
MFA is user-friendly and adaptable to various platforms and services, making it a convenient security measure for individuals and organizations.
Mitigating Credential Theft:
Password breaches and credential theft are common avenues for cyberattacks. MFA mitigates the risk associated with these breaches since an attacker would need more than just a stolen password to access an account.
Protection Against Phishing:
Phishing attacks often involve tricking users into revealing passwords. MFA can thwart these phishing attacks, a sneaky cyber threat since the attacker won’t have the second factor, even if a user’s password is stolen through phishing.
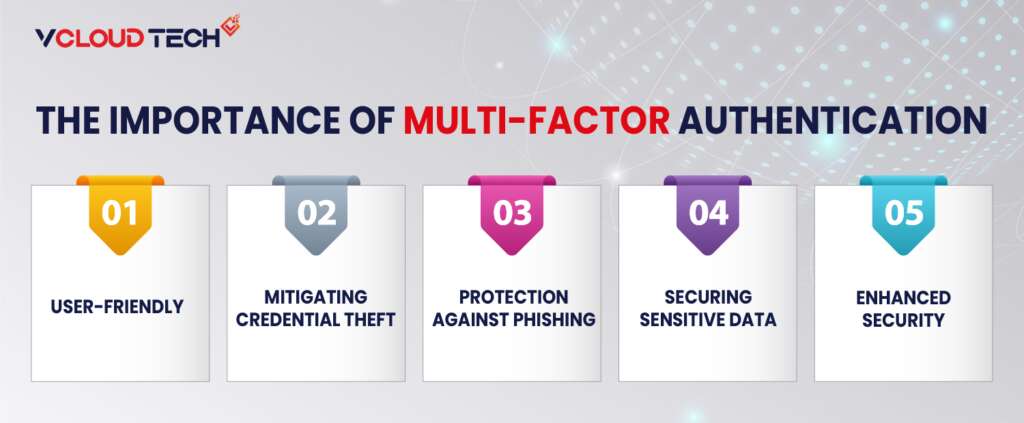
Securing Sensitive Data:
Securing sensitive data and applications is paramount for businesses. MFA ensures only authorized individuals can access critical systems, databases, and confidential information.
Enhanced Security:
MFA significantly bolsters security by adding an extra layer of protection. Even if an attacker obtains a user’s password, they still need the second factor to gain access.
Encouraging the Adoption of MFA:
During Cyber Security Awareness Month, organizations and individuals should promote the adoption of MFA. It is a simple yet highly effective security measure that can prevent unauthorized access and protect against a wide range of cyber threats. Organizations should make MFA a standard practice for accessing corporate systems and applications.
Security Awareness Training
One of the cornerstones of Cybersecurity Education is security awareness training. It equips employees and individuals with the knowledge and skills to recognize and respond to cyber threats. In the corporate world, a well-trained workforce can be the first line of defense against cyberattacks. In Cybersecurity Awareness Month, organizations should prioritize security awareness training to create a culture of cyber vigilance. That includes educating employees about the latest cyber threats, recognizing phishing attempts, and encouraging responsible online behavior.
The Role of Security Awareness Training
Recognizing Common Threats:
Security awareness training equips employees and individuals with the knowledge to identify and understand common cyber threats. That includes recognizing phishing emails, malware, ransomware, social engineering, and other attack vectors.
Safe Online Practices:
Training emphasizes safe online practices, such as using strong, unique passwords, avoiding suspicious websites, and being cautious about sharing personal information. Online Cybersecurity Training also educates individuals about the importance of updating software and applications to patch security vulnerabilities.
Securing Corporate Environments:
Employees are often the first line of defense against cyber threats in a corporate setting. Security Awareness Training ensures employees recognize threats targeting the organization, such as business email compromise (BEC) scams and insider threats. It also teaches them how to report suspicious activities effectively.

Regulatory Compliance:
Many industries and organizations have legal and regulatory requirements related to cybersecurity training. Security awareness training helps organizations comply with these regulations, ensuring they don’t face legal consequences for inadequate security measures.
Cultivating a Culture of Cyber Vigilance:
Cybersecurity is not solely an IT department’s responsibility. It’s everyone’s concern. Security awareness training fosters a culture of cyber vigilance, where everyone protects sensitive information and prevents cyber incidents.
Corporate Security Solutions and Business Risk Management
Businesses are prime targets for cybercriminals due to the valuable data they store and their financial resources. Implementing corporate security solutions and robust business risk management strategies is critical for safeguarding the integrity of enterprises.
Corporate security solutions encompass various tools and practices, including firewall protection, intrusion detection systems, and secure access controls. These measures are essential for defending against cyber threats.
Additionally, businesses should adopt a holistic approach to risk management, identifying potential cyber risks and implementing Security Management to mitigate them. A thorough risk assessment can help organizations prioritize cybersecurity efforts and allocate resources effectively. These solutions encompass a range of tools, practices, and strategies designed to safeguard sensitive data and critical infrastructure. Here are some key components:

Firewalls:
Firewalls act as the first line of defense by monitoring incoming and outgoing network traffic. They help identify and block potentially harmful data packets, preventing unauthorized access and cyberattacks.
Intrusion Detection and Prevention Systems (IDPS):
IDPS are essential for detecting suspicious activities or potential security breaches. Intrusion Prevention analyzes network traffic patterns and behavior to identify anomalies and trigger alerts or actions to mitigate threats.
Secure Access Controls:
Proper access controls ensure that only authorized individuals or systems can access sensitive data or resources. That includes role-based access control, strong authentication, and least privilege principles.
Endpoint Security:
Endpoint Protection Solutions secure individual devices (endpoints) such as laptops, smartphones, and tablets. These solutions provide antivirus, anti-malware, and firewall protection to prevent malicious code from compromising the device.
Encryption:
Data encryption is fundamental in protecting information in transit and at rest. It ensures that even if data is intercepted or stolen, it remains unreadable without the correct decryption key.
Security Information and Event Management (SIEM):
Providing real-time monitoring and analysis of security events, Security Information and Event Management Tools ensure robust security measures. They help organizations identify potential threats and respond quickly.
Security Awareness Training:
While not a traditional security tool, educating employees about cybersecurity best practices is vital to corporate security. Well-trained employees can recognize and report potential threats, reducing the risk of successful attacks.
Business Risk Management: Mitigating Cyber Risks
In the modern business landscape, risk management is integral to ensuring the sustainability and success of an organization. Cybersecurity risks have become a critical part of this equation, and business Cyber Risk Management strategies are necessary to mitigate these risks effectively:
Risk Assessment:
The first step in business risk management is to conduct a comprehensive risk assessment. That involves identifying and evaluating potential cyber risks, including threats, vulnerabilities, and possible consequences.
Risk Mitigation:
Once risks are identified, organizations can develop strategies to mitigate them. That may involve implementing security controls, updating policies and procedures, and enhancing incident response plans.
Incident Response Plan:
Every organization should have a well-defined incident response plan. This plan outlines the steps during a cyber incident, including communication protocols, containment measures, and recovery strategies.

Compliance and Regulations:
Depending on the industry, organizations must comply with various regulations and standards related to data protection and cybersecurity, such as GDPR, HIPAA, or ISO 27001. Business risk management includes ensuring compliance with these regulations.
Insurance:
Cybersecurity insurance is an emerging aspect of business risk management. It can help organizations mitigate the financial impact of a cyber incident. However, it is not a replacement for robust security measures.
Collaboration and Sharing:
Information sharing and collaboration with industry peers can be invaluable in identifying and responding to emerging threats. Collaborative efforts can help organizations stay one step ahead of cybercriminals.
By integrating Corporate Security Operation Solutions and business risk management practices, organizations can create a holistic cybersecurity strategy that protects against known threats and adapts to emerging ones. This approach allows businesses to build resilience, minimize disruptions, and safeguard their reputation in an increasingly digital and interconnected world.
Cyber Security Awareness Month serves as a timely reminder to reinforce these measures and ensure that cybersecurity remains a priority for individual users and businesses. By understanding the significance of corporate security solutions and business risk management, we can collectively strengthen our defenses against cyber threats.
Wrapping up Importance of Cyber Security Awareness:
As we observe Cyber Security Awareness Month, it’s important to recognize that Cybersecurity is a shared responsibility. Individuals, businesses, and governments all have roles to play in securing our digital world. We can strengthen our cyber defenses by focusing on cybersecurity education, data protection, MFA, threat intelligence, security awareness training, and responsible online behavior.
This October, let’s commit to staying safe online, fostering a digital citizenship culture, and taking proactive steps to protect our personal and corporate digital assets. We can secure our digital world and build a safer, more resilient cyber environment.
Reach out to us and book a Free Consultation with vCloud Tech or chat with one of our representatives. Connect with us on Twitter, Facebook, Instagram, and LinkedIn for more information.