A big topic requires Cybersecurity experts to consider every possible entry point a hacker could use to launch an attack. When hackers plan an assault on a company, they first decide what mechanism they will try to exploit. A website, a piece of software, or a networked device are examples. Then they look for ways to carry out their strategy while trying to keep their activities hidden from defense systems. With the ability to be customized, HPE GreenLake Endpoint Security Solutions can guard entire fleets against potential security threats. This helps to safeguard users, the businesses they work for, and the clients they serve.
You’ll need to choose a security solution for each tier of technology after evaluating and categorizing the numerous endpoints on your network. Hardware protection, software protection, Cloud Protection, and network protection are all included. Remember that certain providers may provide a whole portfolio of services to meet your requirements. Finally, you’re ready to execute your chosen solutions and switch to monitoring mode.
What Is Endpoint Security and How It Works?
Endpoint Security protects devices such as desktops, laptops, mobile phones, and tablets from Malicious Threats and Cyberattacks. Endpoint protection software helps organizations Protect Against Cyber Threats on employees’ devices for work on the network or in the cloud. Any endpoint connected to a corporate network represents a vulnerability and provides a potential entry point for cybercriminals. Therefore, employees’ devices connect with business systems and resources, increasing the risk of a hacking pathway. Checkpoint Harmony Endpoint integrates with other products to provide security integration that is centralized and easy-to-use security administration. Its behavior analysis and machine learning algorithms can detect and stop malware before it can cause harm and give highly high catch rates while minimizing false positives.
Malware can exploit devices that can leak or steal sensitive corporate data.
Given this, organizations must deploy Endpoint Solutions that can analyze, detect, block, and contain cyberattacks as they occur. Enterprises must also work together to deploy technologies that enable IT and security teams to gain visibility into advanced threats, quickly identify security risks, and promptly remediate potential issues.
Types of Endpoint Security
The importance of endpoint protection and the variety of endpoints an organization needs to protect has resulted in various endpoint security solutions. Here are some of the most popular types:
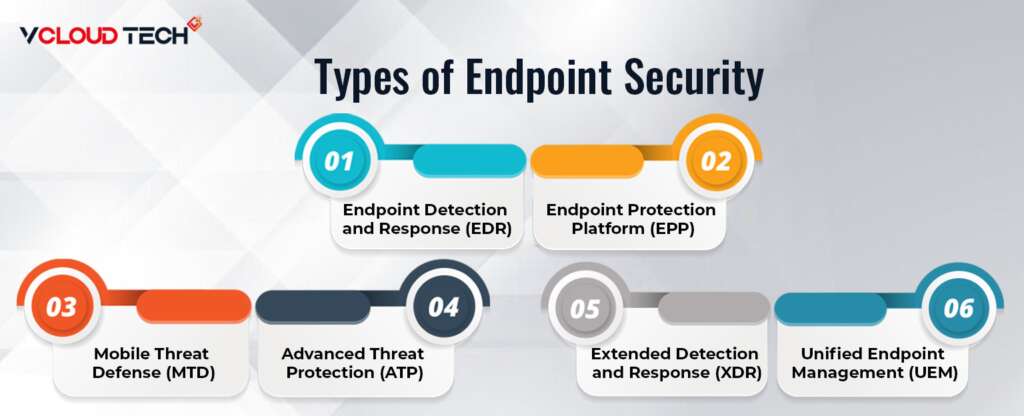
Endpoint Detection and Response (EDR):
EDR solutions aim to provide a comprehensive view of endpoint security threats. Continuous monitoring of multiple data sources combined with endpoint data analytics provides detailed visibility to support the incident investigation, automated response, and threat-hunting activities.
Endpoint Protection Platform (EPP):
EPP solutions serve as the first line of defense for an organization’s endpoints. Identify a wide range of potential Cyber Threats and block them from entering and threatening your endpoints.
Mobile Threat Defense (MTD):
MTD solutions provide endpoint security capabilities targeted at mobile devices and the unique threats they face. MTD tools monitor security misconfigurations and suspicious activity on mobile devices.
Advanced Threat Protection (ATP):
ATP solutions apply advanced security technologies based on Artificial Intelligence (AI) and Machine Learning (ML) to identify and prevent advanced endpoint security threats. Our focus on prevention is to minimize the risk and potential impact of these cyberattacks on your organization.
Extended Detection and Response (XDR):
XDR solutions improve endpoint visibility and threat defense by unifying endpoint security across the enterprise. Consolidating endpoint security monitoring and management into a single dashboard reduces analyst overload, enhances visibility, and accelerates threat detection and response.
Unified Endpoint Management (UEM):
UEM solutions are designed to keep up with the rapid growth of remote devices connected to corporate networks. UEM solutions build on the capabilities of Mobile Device Management (MDM) solutions to provide comprehensive monitoring and control of remote devices, supporting Desktop Virtualization, laptops, and mobile devices.
Each endpoint in your organization’s network may have different security requirements. However, the wide variety of Endpoint Security Services allows businesses to implement strong security on their corporate networks.
Endpoint Security Component:
Endpoint security solutions can include various features that protect against cyber threats. Essential components of its architecture include:
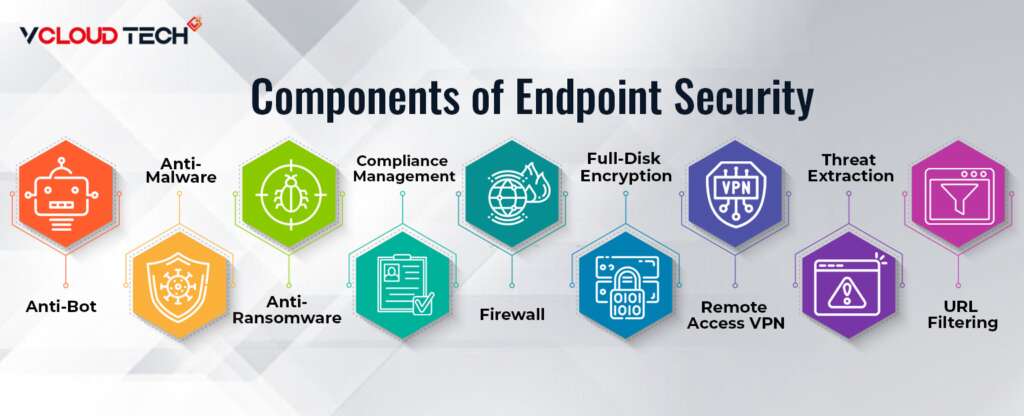
- Anti-Bot: Identify and block botnet commands, control infected computer traffic, and gain botnet malware visibility.
- Antimalware: Uses a combination of signatures and Malwarebytes Endpoint Protection anomaly to identify and remediate malware infections.
- Anti-Ransomware: Detects ransomware through behavioral analysis and detection of known ransomware operations such as Modifying Registry Values.
- Compliance Management: Enforce company compliance policies. Ensure that security tools are working and limit the software that can run on your system.
- Firewall: inspects network traffic to and from endpoints and enforces application-specific security policies.
- Full-Disk Encryption: Encrypts entire device storage to prevent data access without knowing user credentials. Removable Media Protection: Restricts USB port usage and encrypts all data stored on removable media.
- Remote Access VPN: Provides a secure, encrypted connection to corporate networks and resources.
- Threat Extraction: Use Content Disarm and Reconstruction (CDR) capabilities to remove malicious content from documents and grant users access to sanitized documents.
- URL Filtering: Organizations can block browsing to websites that are malicious or do not comply with company policies.
What are the Benefits of Endpoint Security for Businesses?
Local networks had very defined and rigorous perimeters in the early days of the internet when organizations were only starting to embrace new computing technologies in their workplaces. You must be physically in the same workplace and use the same portal to access central repositories and servers. Trend Micro Endpoint Security with Apex One cybersecurity solution gives organizations actionable insights, increased investigative capabilities, and unified visibility using an advanced strong SIEM integration, EDR toolset, and an open API set. The situation is entirely different with the change to Cloud Hosting and Software-as-a-Service in the modern workplace. Employees, partners, and vendors are all using their own devices to connect to your company network, many of which are in remote locations. The following are some benefits:
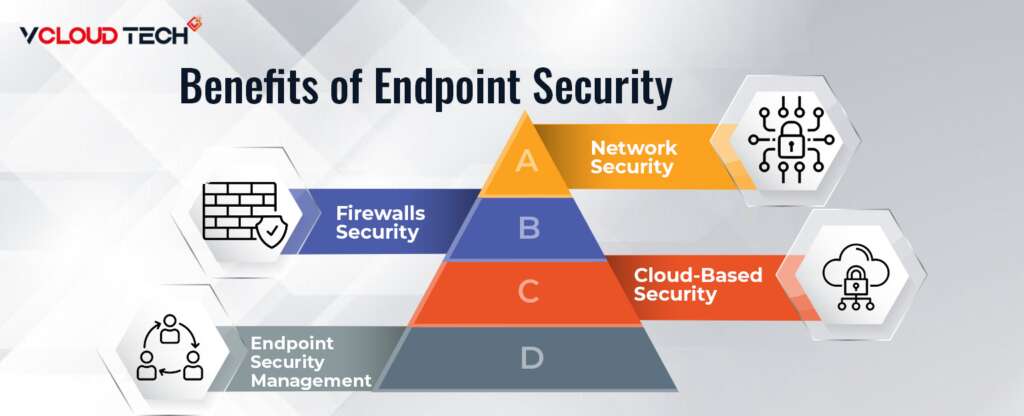
Network Security:
It’s easy to imagine a computer network as a road map of a city. Each path allows individuals – or data packets in this example – to travel from one location to another. Some highways are faster than others and allow travel outside of the city. Defining the boundary of your local network when it comes to endpoint security is critical. This saves network bandwidth and allows Office 365 Backups to be performed even on slow cellular networks.
The local network should house your company’s virtual servers, databases, and applications. They may be dispersed over numerous cloud infrastructure components, but thanks to the wonders of IP addressing, they can all be controlled from within a single network. Endpoint security necessitates examining the perimeter of your Network Virtualization and tracing every incoming connection that tries to breach that barrier. Each request view as a threat to endpoint security, regardless of the type of device or user that makes it.
Firewalls Security:
Firewalls were typically hardware devices directly connected to your leading network portal in the early days of the internet. The majority of today’s Firewall Systems are software-based. Still, they all have the same goal: to monitor all incoming web traffic and filter out specific IP addresses based on user-defined regulations. Unfortunately, some businesses make the mistake of believing that a robust firewall can provide comprehensive endpoint security. That is not the case, particularly in firms where many employees work remotely. These external connections, which a firewall cannot constantly monitor or manage, must be factored into a whole endpoint security plan.
Cloud-Based Security:
The Cloud Computing Revolution has brought many advantages to software companies. You can rent computing power from a cloud-hosting provider instead of wasting time, money, and resources managing and maintaining local servers or data centers. However, the complexity of cloud-based infrastructure increases. Every level of access in your cloud architecture is a new endpoint that needs security.
Endpoint Security Management:
As previously mentioned, antivirus technologies that run on a single device usually require minimum maintenance and function in the background without user intervention. That is different from full-fledged endpoint security solutions. The monitoring and maintenance of these systems frequently necessitate the involvement of a specialist IT team. Businesses of Endpoint Security must conceive as a continuous process. Blocking a specific piece of malware or a suspect IP address is insufficient to guarantee future security. Endpoint security administrators must be ready to tune and change their tools to stay safe as hackers and cybercriminals develop new attacks.
Reach out to us and book a Free Consultation with vCloud Tech or chat with one of our representatives. Connect with us on Twitter, Facebook, Instagram, and LinkedIn for more information.