Advancements and Challenges
Deep Packet Inspection (DPI) is a technology for analyzing and filtering network traffic. With the increasing number of internet-connected devices, network traffic has increased exponentially. Therefore, DPI is critical in Network Security, management, and revenue generation of Internet Service Providers (ISPs). In this article, we will discuss the advancements and challenges of DPI and its impact on network security and management.
What is Deep Packet Inspection?
DPI is a technology used for analyzing and filtering network traffic. Deep Packet Inspection analyzes the data packets transmitted over the network and extracts information from them, such as the type of application, the protocol used, and the packet’s content. As a result, DPI can identify the source and destination of the packet, the type of data transmitted, and any malicious content.
The internet has become an integral part of our lives, and we rely on it for communication, entertainment, and work. However, with the rise of cyber threats, network security has become a primary concern for businesses, governments, and individuals. Deep Packet Inspection (DPI) is a technology used for analyzing and filtering network traffic, making it an essential tool for Network Management and security.
How Deep Packet Inspection Works?
Deep packet inspection (also known as DPI) is a type of packet filtering that is often carried out by firewalls. This pertains to the application layer of the Open Systems Interconnection protocol.
Deep packet inspection is a form of content analysis that is performed on data packets after they have passed through inspection points. For the purpose of determining how to deal with those packets in real time, deep packet inspection makes use of rules that are assigned either by you, your Internet Service Provider (ISP), or your network or system administrator.
The contents of these packets are analyzed by deep Packet inspection, which also has the capability of locating the origin of the packets, such as the service or application that was responsible for sending them. In addition, it can collaborate with filters to identify and reroute network traffic coming from specified IP addresses or online services like Twitter and Facebook.
Deep Packet Inspection and Conventional Packet Filtering
The packet’s header information of each packet is the sole thing that is read by traditional methods of packet filtering. Because of the technical constraints that existed at the time, that method of filtering packets was a lot less complicated and more basic than modern methods of doing the same thing. The firewall had a limited amount of processing power and required more in order to handle a large number of packets. To put it another way, conventional packet filtering is analogous to reading the title of a book without knowing what’s on the cover or analyzing the content of the book.
Deep packet inspection is now a practical possibility as a result of the development of new technologies. As it became more comprehensive and exhaustive, it became analogous to taking up a book, opening it, and reading it from the very first page to the very last page.
Advancements in Deep Packet Inspection
DPI has evolved significantly in recent years, with new advancements and improvements that have made it more efficient and effective. Some of the advances in DPI are:
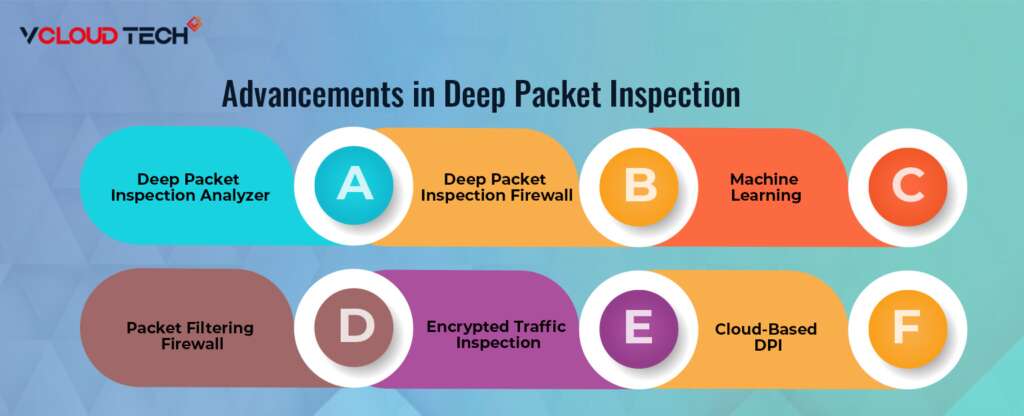
Deep Packet Inspection Analyzer
DPI Analyzer is a software tool used for analyzing network traffic. It can capture and analyze packets in real time, providing insights into network performance, security threats, and application usage. DPI Analyzer is an essential tool for network administrators and security professionals, as it helps them monitor and Manage Networks effectively. The evolution of technology has brought about many advancements in DPI. As a result, DPI analyzers are becoming more powerful and accurate, allowing ISPs to identify and analyze network traffic with greater precision. That will enable ISPs to identify more types of traffic, including encrypted traffic, which was previously difficult to locate.
Deep Packet Inspection Firewall
A Deep Packet Inspection Firewall is a type of firewall that uses DPI technology to inspect network traffic. DPI Firewalls can identify and block malicious traffic, such as viruses, malware, and spam, and provide a higher level of security than traditional firewalls. These firewalls use DPI tools to identify and block malicious traffic, ensuring that only authorized traffic is allowed on the network. Barracuda CloudGen Firewall also enables ISPs to identify and prioritize different types of traffic, optimizing their networks for performance.
Packet Filtering Firewall
Packet Filtering Firewall is a type of firewall that filters network traffic based on predefined rules. For example, it can block or allow packets based on the source and destination IP addresses, port numbers, and protocol. Packet Filtering Firewall is less effective than DPI Firewalls, as it cannot identify the type of application or content of the packet.
Machine Learning
DPI systems can now incorporate machine learning algorithms to identify patterns in network traffic and distinguish between legitimate and malicious traffic more accurately. That has dramatically improved the ability of DPI to detect and prevent advanced threats.
Cloud-Based DPI
With the increasing adoption of cloud-based services, Fortinet FortiGate NGFW systems have adapted to monitor traffic across multiple cloud platforms. That enables organizations to maintain visibility into network traffic, regardless of where it originates.
Encrypted Traffic Inspection
DPI technology can now inspect encrypted traffic using SSL/TLS. In addition, DPI can detect and prevent threats hidden within encrypted traffic by decrypting traffic in real time.
Challenges for Deep Packet Inspection
Deep Packet Inspection (DPI) is a method of analyzing and monitoring network traffic, but it comes with several challenges. Here are some of the challenges faced while implementing DPI:

Performance:
DPI requires analyzing every packet that passes through the network, which can increase latency, especially in high-speed networks. Ensuring that DPI does not negatively impact network performance can be challenging.
Privacy Concerns:
DPI raises privacy concerns since it involves examining the contents of network traffic, including personal and sensitive information. Balancing the need for network security with users’ privacy can be a challenge.
Encryption:
Encrypted traffic is becoming increasingly common, making analyzing and monitoring network traffic challenging. DPI tools must be able to decrypt traffic to perform analysis, but this can be not easy without the appropriate keys or permissions.
Protocol Support:
DPI must support all the network protocols to be effective. As new protocols emerge, DPI tools must be updated to support them.
False Positives and Negatives:
DPI can generate false positives and negatives, leading to unnecessary alerts or missed threats. To ensure the effectiveness of DPI, it is crucial to minimize false positives and negatives while still detecting genuine threats.
Scale:
DPI must be able to handle large volumes of network traffic, especially in enterprise-level networks. Scaling DPI to handle high volumes of traffic can be a significant challenge.
Complexity:
DPI can be complex to implement and maintain, requiring specialized knowledge and skills. This complexity can make troubleshooting issues challenging and ensure that DPI operates correctly.
How to Overcome these Challenges?
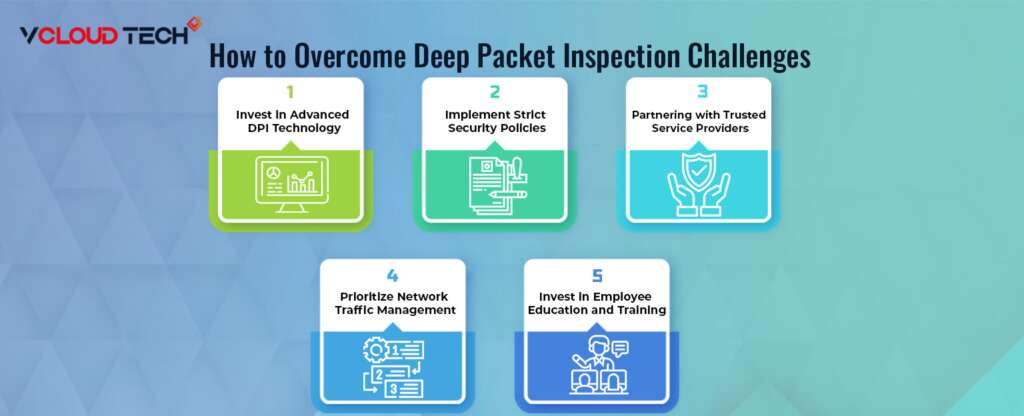
Invest in Advanced DPI Technology:
One of the most effective ways to overcome the challenges of DPI is to invest in the latest and most advanced DPI technology. That includes hardware and software solutions specifically designed to handle the increased complexity and volume of network traffic and machine learning algorithms that can detect and prevent malicious activity.
Implement Strict Security Policies:
To ensure that your network remains secure, it is essential to establish strict security policies that govern how it is managed and accessed. Check Point SandBlast provides policies around password management, access control, and data encryption, as well as regular security audits to identify and address any vulnerabilities in your network.
Partnering with Trusted Service Providers:
Another way to overcome the challenges of DPI is to partner with trusted service providers specializing in network security and management. These providers can help you implement the latest security solutions and best practices and provide ongoing support and monitoring to ensure your network remains secure and stable.
Prioritize Network Traffic Management:
With the increasing volume of network traffic, it is essential to prioritize Network Traffic Management to ensure that critical applications and services receive the bandwidth and resources they need to function correctly. That includes implementing traffic shaping and prioritization policies and deploying advanced DPI tools to identify and manage network traffic in real time.
Invest in Employee Education and Training:
Finally, it is essential to invest in employee education and training to ensure that your staff understands the importance of network security and the role that DPI plays in keeping your network secure. That includes regular training sessions, workshops, ongoing communication, and reminders about best practices and security policies.
By following these strategies, you can overcome the challenges of DPI and ensure that your network remains secure, stable, and optimized for the growing demands of network traffic.
Reach out to us and book a Free Consultation with vCloud Tech or chat with one of our representatives. Connect with us on Twitter, Facebook, Instagram, and LinkedIn for more information.